Making Third Party Data Relationships Safe
 Third parties are a critical component in the data supply chain. They can also be a weak point in data governance plans.How do you ensure your partners’ processes are compliant, without slowing down the flow of data? Third parties can be the great unknown in data governance. They are often at the root of quality, security and compliance problems with data.
Third parties are a critical component in the data supply chain. They can also be a weak point in data governance plans.How do you ensure your partners’ processes are compliant, without slowing down the flow of data? Third parties can be the great unknown in data governance. They are often at the root of quality, security and compliance problems with data.
The Ponemon Institute has reported that third parties account for one third of all data security breaches. Make no mistake - your data remains your responsibility when transferred to a third party, both in the eyes of customers, who will view any lapse as yours, and in the eyes of the legislator.
There are four key risks from third party data transfers:
1.Your data may be lost accidentally.
2.Your data may be deliberately targeted and stolen.
3.The third party may compromise your compliance with the Data Protection Act or other regulations through careless or inappropriate use of your data.
4.The quality and accuracy of your data may be compromised.
All of these breaches have the potential for a significant loss of customer trust, loyalty and revenue. Research from the Ponemon Institute shows that there is an average 3.9 per cent customer churn following any data breach and an average of £29 lost business for each individual record lost.
Secondly, there is the threat of regulatory fines, with the Information Commissioner now having the power to levy charges up to £500,000 and other regulators able to impose unlimited financial sanctions. Zurich Insurance & Accidental Loss discovered this in 2010 when it was fined a record £2.27 million by the Financial Services Authority for the loss of 46,000 customer records.
Zurich had outsourced the processing of some of its customer data to a Zurich group company in South Africa. In August 2008, that division lost an unencrypted back-up tape during a routine transfer to a data storage centre. Because it did not have adequate reporting lines in place, Zurich UK did not learn of the incident until a year later. The FSA concluded that the company, “failed to…ensure it had effective systems and controls to manage the risks relating to the security of customer data resulting from the outsourcing arrangement.”
Adverse publicity will have a further significant impact on the brand, leading to further loss of customer trust, loyalty and business.Lastly, there is considerable cost in addressing the immediate problem through the need for advice notices to customers, help lines to answer queries, briefings to customer-facing staff, additional PR and the staff time taken to address and control the issue.
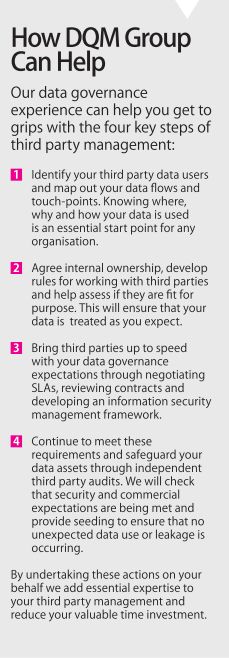
Four Steps to Control Third Parties
Step one: Map your data flows and touch points
 Identify what data you hold - establishing the location and accesses permitted to all the caches of data throughout the organisation can in itself be a revealing and valuable exercise. Next, who has access to your on-site data? Which employees, in which areas of the organisation? Is data also distributed to branches, franchises or other group companies? What scope does each of these internal users have to pass data on to external third parties and what controls are in place?
Identify what data you hold - establishing the location and accesses permitted to all the caches of data throughout the organisation can in itself be a revealing and valuable exercise. Next, who has access to your on-site data? Which employees, in which areas of the organisation? Is data also distributed to branches, franchises or other group companies? What scope does each of these internal users have to pass data on to external third parties and what controls are in place?
Next, who do you send data to for business services? Destinations could include call centres, computer bureaux, printers and mailing houses, as well as external email marketing or analytics providers. What levels of confidence do you have in their security and controls? There may be others, for example, previously-contracted third parties with whom you no longer have a relationship but who might still hold historical data or, perhaps worse, still have access.
Identifying all the third parties who have access or potential access to your data can be a disconcerting process. A recent Royal Bank of Scotland audit discovered over 850 third parties around the world – an extended network ranging from bank statement printers to computer hardware providers, from publishers and payroll processors to cash logistics firms and lawyers.
Step two: Set internal rules and standards
As a minimum this process should consider:
•How each third party is managed and by whom. Someone must be responsible for managing the third party relationship throughout its lifetime and for ensuring that appropriate contracts and Service Level Agreements (SLAs) are in place.
•The objective of supplying the data to a third party. Be very clear internally and with each third party why the data is being supplied and how the third party is permitted to use the data.
•How much data will be released. Provide each third party with the minimum depth and volume of data required to achieve their objectives. Good data governance starts with minimisation - ensuring that as little data as possible is provided to as few people as possible for as little time as possible.
•How the data will be provided. The distribution method should reflect the volume and sensitivity of the data in transit and should mandate how the data will be returned.
•How you will monitor third party use of your data.
Step three: Set rules for third parties
Ensure that your expectations and requirements are fully understood and agreed across all your third parties via contracts and SLAs.
Contracts should stipulate:
•Compliance with the Data Protection Act, Privacy in Electronic Communications Regulations and any other applicable legislation - remember that the buck stops with the data controller not the processor.
•The right to audit third party activities and to use data seeding to monitor use.
•Termination clauses - what will happen to your data when the contract is terminated?
•Rules and requirements relating to the people, processes and technology used in delivering the service.
SLAs should include the following:
•Names or roles of individuals that will have access to your data. You might stipulate that temporary or contract staff may not have access without express permission.
•Any change of personnel must be communicated within an agreed timeframe. 
•Training and security awareness for these employees.
•Limits on the number of individuals who have access to your data. Consider, too, how access rights are withdrawn when someone leaves or changes role.
•Documentation of data operating procedures and processes. This serves two key functions: you can confirm that they understand your instructions, plus you’ll be more confident that those instructions are passed on to the third party delivery team correctly.
•The number of copies of your data and, very importantly, how long these may be retained. If copies proliferate unchecked, returning or deleting them at the end of the contract may prove impossible.
•That data no longer required should be clearly marked and returned or securely destroyed. The third party should be able to account for every copy or version of your data at periodic intervals or on contract termination.
•Restrictions on any further outsourcing of activity, or at the very least require that your permission be given for any further third party usage.
•Technical security controls in line with your organisation’s own security practices.These should include physical and environmental security controls, such as restricting access to the areas where your data is held; the use of controls such as firewalls and anti-virus protection; how the restrictions on who can access your data are implemented and the robustness of this process, including what kind of access logs are in place, how long they are retained and how often they are reviewed for unauthorised activity.
•How many back-ups the third party is allowed or required to take and at what intervals.
Consider also what will happen in the event of contract termination. In certain instances, you may mandate that your data must be backed-up and retained separately from any other data held by the third party.
 Case Study: Skipton Data Error
Case Study: Skipton Data Error
In January 2010, Skipton Building Society was forced to apologise to customers after a breach of data security procedures resulted in thousands of savers receiving financial details about other customers in an account statement mailing. The building society said a third party printing error led to the account details of 3,115 customers being printed on the back of other people’s statements.
The ICO took a dim view, stating: “Even when the breach occurs as a result of third parties processing personal information, the data controller…should ensure the necessary security policies and procedures are in place and that all employees are made aware of them."
Step 4: Check that they play by the rules
All contracts with third parties should give you the right of audit. You should audit to check that their care and use of the data corresponds to the contract and SLA. In a perfect world, you would audit all third parties at the start of the working relationship and then on a regular basis, although this will vary according to the volume and complexity of third party relationships that your organisation might have.
Where complete coverage is impossible, aim to target those third parties which pose the greatest risk - those who have access to the most sensitive or valuable data, those where you have had problems in the past, or those with whom you work most frequently. Audit objectives are not punitive, but simply to ensure that issues are identified and fixed within an agreed timescale.
To underpin this audit program you should also seed your data. Seeding provides an early warning of any abuse of your data and proof of misuse, giving you the opportunity to enforce compliance or even prosecute if necessary. Publicise your use of seeds and describe it in your contracts, ensuring that third parties understand that the data is being monitored.
Did you find this content useful?
Thank you for your input
Thank you for your feedback
You may also be interested in
DataIQ is a trading name of IQ Data Group Limited
10 York Road, London, SE1 7ND
Phone: +44 020 3821 5665
Registered in England: 9900834
Copyright © IQ Data Group Limited 2024




